NetGladiator is part of an overall Layered Security Approach. Learn more about Layered Security and how the NetGladiator fits in that approach. Review our Key Benefits, our Core Capabilities, and the Hardware Options available. For even more details, read our NetGladiator Data Sheet. At the Perimeter Level, NetGladiator implements Filtering and P2P Blocking security measures. At the Network Level, NetGladiator is inspecting Internet traffic across the network, which we call Traffic Pattern Blocking. If traffic patterns match defined NetGladiator patterns, whether P2P or web-application specific, traffic from the IP will be blocked. At the Hosts level, we provide Web Application Security by protecting your web servers from hackers and botnets. Any web application that has even a small amount of interactivity or back-end to it will benefit from NetGladiator’s features. NetGladiator uses Custom Patterns to block traffic specific to your environment. We support patterns looking for both time-based anomalies and repetitive behaviors, aligned with the Top 10 Application Security Risks from the Open Web Application Security Project (OWASP Top 10). We quickly check for key patterns that show malicious intent under the assumption that those patterns will be tried eventually by an attacker. This way, data can seamlessly pass through, and your users will not incur performance problems. As part of the installation process, we offer a service which we believe is unique in the IPS space. We have security experts who are also white knights (friendly hackers) perform a Baseline Security Assessment to customize your NetGladiator configuration. Our white knights think through the information discovery process in the same way that a hacker would, enabling them to establish the correct set-up to thwart hackers. Because NetGladiator is custom-configured for your environment, you are alerted on meaningful intrusion attempts without false positive alerts. You do not need a team of IT people to sift through alerts, read reports, and make adjustments. (back to top)
Layered Security Approach
Benefits
Core Capabilities
Hardware Options
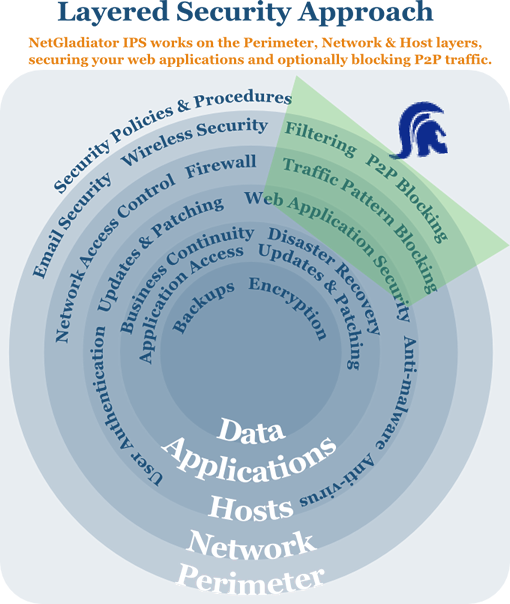 A Layered Security Approach recognizes that in order to maximize effectiveness, prevention measures must be implemented across a variety of security areas and at all architecture levels. In our diagram, you can see that NetGladiator operates on three levels: Perimeter, Network, and Host.
A Layered Security Approach recognizes that in order to maximize effectiveness, prevention measures must be implemented across a variety of security areas and at all architecture levels. In our diagram, you can see that NetGladiator operates on three levels: Perimeter, Network, and Host.
Key Features & Specifications
NetGladiator Data Sheet

Benefits (back to top)
Features
Core Capabilities (back to top)
Intrusion Detection
Customized configuration to define patterns for your environment.
1) Time-sensitive anomalies
2) Traffic anomalies
Intrusion Alerting
Notifications are emailed with assigned severity.
1) Level 1 (suspicious)
2) Level 2 (hack)
Intrusion Prevention
Anomalies are logged and blocked, stopping hackers during their information discovery process.
1) Level 1 logs the activity
2) Level 2 logs & blocks the activity
Prevents these Types of
Web Application Breaches
Persistent cross-site scripting (OWASP Top 10)
Reflected HTTP redirects (OWASP Top 10)
Reflected cross-site scripting (OWASP Top 10)
URL SQL injection (OWASP Top 10)
Administrative interface login brute forcing
Denial of Service (DoS) attacks
Directory Traversal
Login brute forcing
And more...
Logging
Logs all Level 1 and Level 2 activity.
Reporting
1) Blocked IPs
2) Suspicious IPs
Customized Configuration
NetGladiator IPS is installed between your firewall and your enterprise. Once your patterns are defined through our security assessment process, it is a quick and easy set-up process.
Hardware Options (back to top)
For more information, contact Sales at 303.997.1300 x123 or ips@apconnections.net